Blitzkrieg Alberta
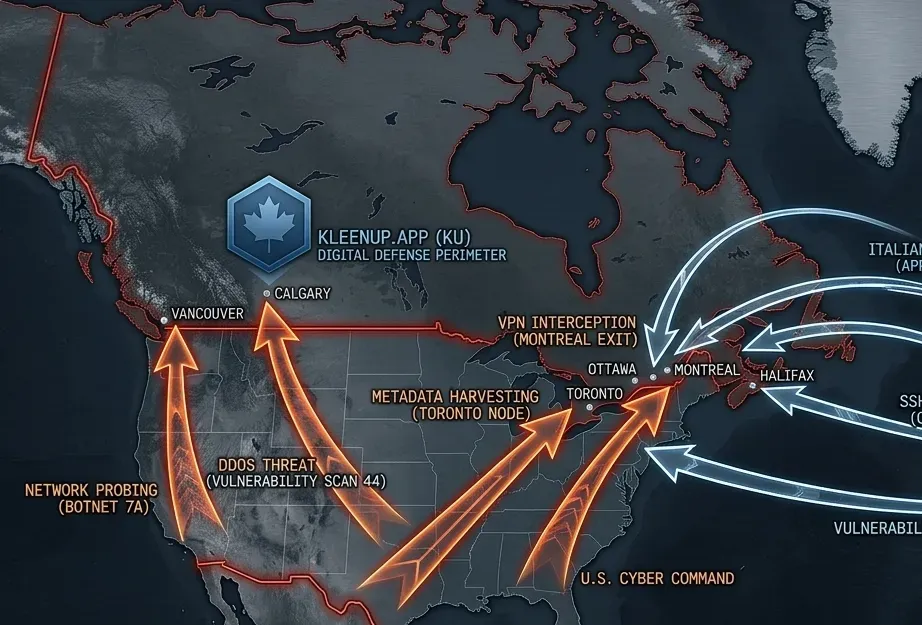
Did the UCP just paint a target on Canadians? In a polarized Weird War world to state level hackers with sophisticated tools like AI, this is a dream come true, they can now launch the first of many technological Blitzkrieg's. To "Hack" people -disrupt their lives, cause psychological and financial harms, threat actors first need to acquire data, where they live (IP addresses), names, and the targets behavior, you can learn a lot from this data, most importantly voting intentions, which side they're on. The Hackers Dream ... The Alberta Voter List Leak (The Centurion Project) The massive data breach and gathering the Data What Happened: An Alberta separatist organization called The Centurion Project (founded by political operative David Parker) built an app and an online, searchable database containing the personal information of nearly 3 million Albertans —essentially the entire provincial list of electors, including names, physical addresses, and phone numbers. The Source: Elections Alberta traced the leaked data directly back to a legitimate copy of the voter list that had been legally provided to the pro-independence Republican Party of Alberta . Somehow, that data was transferred to the Centurion Project to help them track down and recruit separatist supporters. The Current Fallout: Elections Alberta secured a court injunction to force the database offline, and three separate investigations are actively underway by the RCMP, Elections Alberta, and the provincial Privacy Commissioner. Over 550 cease-and-desist letters have been sent to individuals who accessed or downloaded the data, but as security experts have pointed out, once a file that size is exposed to political operatives and bad actors, it is incredibly difficult to completely claw back. It is absolutely a "hacker's dream" and a public safety disaster, because an organized, highly politicized database of citizens' physical addresses is now out in the wild. The Threat: Big Tech, Telus, and Surveillance Systems The Palantir & Telus Connection: There is growing public scrutiny over telecom giants like Telus partnering with big-data analytics and defense firms like Palantir, alongside Telus's push into building "Sovereign AI" infrastructure and data centers. Palantir's core business model is mass data aggregation and predictive analysis—software built for intelligence agencies—so when it integrates with domestic telecommunications infrastructure, it naturally raises massive red flags about tracking, data silos, and user privacy and weaponizing information. The Citizen Lab Reports: The Citizen Lab (out of the University of Toronto) recently published a major policy brief explicitly warning about transnational repression in Canada. Their research emphasizes that Canada's uncritical embrace of powerful artificial intelligence tools and corporate surveillance tech is actively leaving communities and political dissidents vulnerable to digital targeting, harassment, and tracking by both foreign actors and domestic data abuses. Grounding Your Digital Defense When the political landscape of hostile news confirms that big data is being mishandled, the most effective thing you can do to reclaim your peace of mind is to lock down your personal digital perimeter. Since you can't control what political parties or telecoms do with data aggregates, focus heavily on Zero-Trust principles for your immediate world: Audit Content Exposure: If you run self-hosted infrastructure, Docker containers, or personal websites, make sure your reverse proxies (like Nginx Proxy Manager) and Cloudflare tunnels are explicitly hardened to hide your home IP address entirely behind a proxy. Harden the Perimeter: Ensure your local firewall (UFW) is strictly configured to drop all unsolicited inbound traffic by default, allowing only explicitly defined ports. De-link Public Data: Since phone numbers and physical addresses from the voter registry are compromised, assume that basic phishing, targeted spam, or social engineering attempts across Alberta will rise. Treat unexpected communications with a high degree of skepticism. It is a volatile time to have a voice in the province, and seeing these systems converge is real. The Canadian Government must act to guard it's citizens from threats foreign or domestic, Prime Minister Carney needs to act now. Of course we have nothing to protect us but a fraud website and an underfunded and politically targeted (by the UCP) federal police force, the RCMP... https://rcmp.ca/en/federal-policing/cybercrime/national-cybercrime-coordination-centre https://reportcyberandfraud.canada.ca/ speak up, speak out and protect yourselves it looks like this war is just starting.
Read More